Honouring Our Pledge to Trust, Innovation and Community at GovWare
In 2023, we refreshed our brand identity to embody a renewed vision that encapsulates the vibrant interplay at GovWare – a representation of the convergence of great minds, ideas and innovation, signifying the dynamic pulse of our community.
GovWare is more than a cybersecurity information platform; it's a commitment to driving connectivity, collaboration, and trust within today’s hyper-connected ecosystem of government, industry, and enterprise. It's about collectively securing our innovation and digitalisation journey for a future that knows no bounds.
We are GovWare – where cyber means business.
GovWare, the region’s premier cybersecurity information and connectivity platform, offers multi-channel touchpoints to drive community intel sharing, training and strategic collaborations.
A trusted nexus for over two decades, GovWare unites policymakers, tech innovators and end-users across Asia and beyond, driving pertinent dialogues on the latest trends and critical information flow. We empower growth and innovation through collective insights, partnerships and connections.
Our success lies in the trust and support from the cybersecurity community that we have had the privilege to serve over the years, as well as organisational partners that share the same value and mission to enrich the cybersecurity ecosystem.
Speak to us and find out more about how we can help you connect with the region’s most robust cyber community.
Upcoming Events
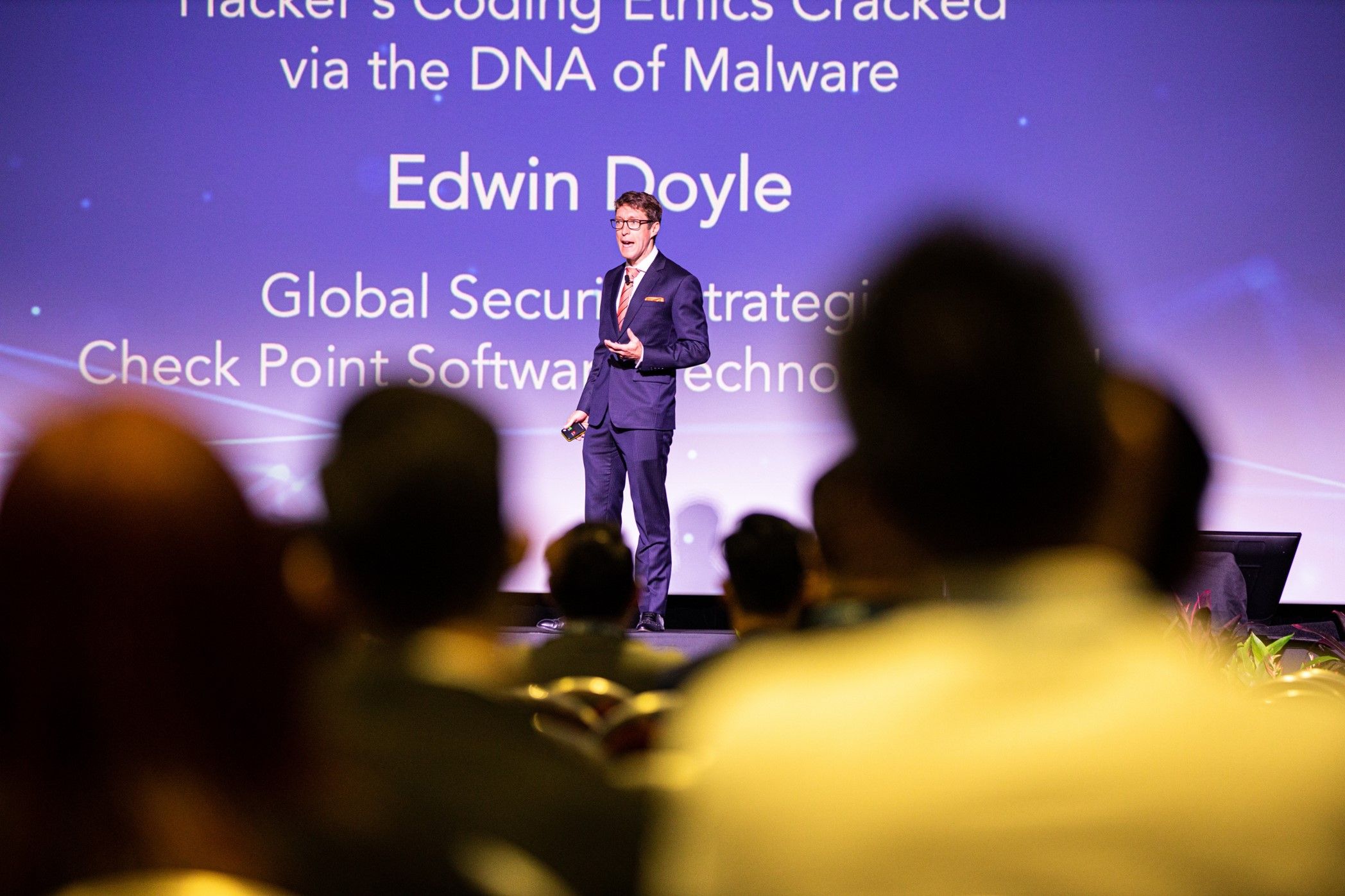
GovWare Conference and Exhibition
Join over 12,000 policymakers, cybersecurity leaders, and practitioners at GovWare 2024! The global cyber community gathers to explore cutting-edge tech, build connections and form partnerships.
Save the date for GovWare 2024 from 15-17 October – register your interest now to save S$700!
Have an interesting proposition that drives cyber leadership forward? Make your submission now for the Call for Speakers.
GovWare Focus Series
The GovWare Focus Series is designed to deliver impactful dialogues on specific cybersecurity tech focus or industry verticals.
These smaller-scale sessions keep the conversation going all year round, bringing together experts and decision-makers to shape norms, policies and collective strategies to pave the way for a secure and resilient digital world.

Connecting the Community, Safely and Purposefully
The health and safety of our staff, partners and attendees are our utmost priority. We are committed to delivering a safe and meaningful experience for the community. Our team works closely with the Singapore Tourism Board – the regulatory body for MICE, as well as our venue and service vendors to ensure that expert guidance from relevant Singapore national agencies is incorporated in our event design and safety plan.

IMPORTANT NOTICE
Please be aware of fraudulent emails offering GovWare's attendee lists for purchase. We will never sell the personal data of our show attendees. We encourage everyone to check our official channels or contact us for GovWare's official partners and offers.
If you receive one of these emails, please do not respond and forward it to [email protected], or contact your GovWare representative.